WordPress Astra Theme Vulnerability Affects +1 Million Sites via @sejournal, @martinibuster
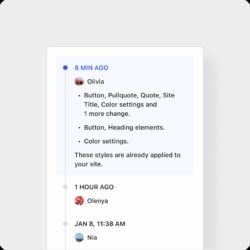
One of the World’s most popular WordPress themes quietly patched a security vulnerability over the weekend that security researchers say appears to have patch a stored XSS vulnerability.
The official Astra changelog offered this explanation of the security release:
“Enhanced Security: Our codebase has been strengthened to further protect your website.”
Their changelog, which documents changes to the code that’s included in every update, offers no information about what the vulnerability was or the severity of it. Theme users thus can’t make an informed decision as to whether to update their theme as soon as possible or to conduct tests first before updating to insure that the updated theme is compatible with other plugins in use.
SEJ reached out to the Patchstack WordPress security company who verified that Astra may have patched a cross-site scripting vulnerability.
Brainstorm Force Astra WordPress Theme
Astra is one of the world’s most popular WordPress theme. It’s a free theme that’s relatively lightweight, easy to use and results in professional looking websites. It even has Schema.org structured data integrated within it.
Cross-Site Scripting Vulnerability (XSS)
A cross-site scripting vulnerability is one of the most common type of vulnerabilities found on WordPress that generally arises within third party plugins and themes. It’s a vulnerability that occurs when there’s a way to input data but the plugin or theme doesn’t sufficiently filter what’s being input or output which can subsequently allow an attacker to upload a malicious payload.
This particular vulnerability is called a stored XSS. A stored XSS is so-called because it involves directly uploading the payload to the website server and stored.
The non-profit Open Worldwide Application Security Project (OWASP) website offers the following description of a stored XSS vulnerability:
“Stored attacks are those where the injected script is permanently stored on the target servers, such as in a database, in a message forum, visitor log, comment field, etc. The victim then retrieves the malicious script from the server when it requests the stored information. Stored XSS is also sometimes referred to as Persistent or Type-II XSS.”
Patchstack Review Of Plugin
SEJ contacted Patchstack who promptly reviewed the changed files and identified a possible theme security issue in three WordPress functions. WordPress functions are code that can change how WordPress features behave such as changing how long an excerpt is. Functions can add customizations and introduce new features to a theme.
Patchstack explained their findings:
“I downloaded version 4.6.9 and 4.6.8 (free version) from the WordPress.org repository and checked the differences.
It seems that several functions have had a change made to them to escape the return value from the WordPress function get_the_author.
This function prints the “display_name” property of a user, which could contain something malicious to end up with a cross-site scripting vulnerability if printed directly without using any output escaping function.
The following functions have had this change made to them:
astra_archive_page_info astra_post_author_name astra_post_authorIf, for example, a contributor wrote a post and this contributor changes their display name to contain a malicious payload, this malicious payload will be executed when a visitor visits that page with their malicious display name.”
Untrusted data in the context of XSS vulnerabilities in WordPress can happen where a user is able to input data.
These processes are called Sanitization, Validation, and Escaping, three ways of securing a WordPress website.
Sanitization can be said to be a process that filters input data. Validation is the process of checking what’s input to determine if it’s exactly what’s expected, like text instead of code. Escaping output makes sure that anything that’s output, such as user input or database content, is safe to display in the browser.
WordPress security company Patchstack identified changes to functions that escape data which in turn gives clues as to what the vulnerability is and how it was fixed.
Patchstack Security Advisory
It’s unknown whether a third party security researcher discovered the vulnerability or if Brainstorm, the makers of the Astra theme, discovered it themselves and patched it.
The official Patchstack advisory offered this information:
“An unknown person discovered and reported this Cross Site Scripting (XSS) vulnerability in WordPress Astra Theme. This could allow a malicious actor to inject malicious scripts, such as redirects, advertisements, and other HTML payloads into your website which will be executed when guests visit your site. This vulnerability has been fixed in version 4.6.9.”
Patchstack assessed the vulnerability as a medium threat and assigned it a score of 6.5 on a scale of 1 – 10.
Wordfence Security Advisory
Wordfence also just published a security advisory. They analyzed the Astra files and concluded:
“The Astra theme for WordPress is vulnerable to Stored Cross-Site Scripting via a user’s display name in all versions up to, and including, 4.6.8 due to insufficient input sanitization and output escaping. This makes it possible for authenticated attackers, with contributor-level access and above, to inject arbitrary web scripts in pages that will execute whenever a user accesses an injected page.”
It’s generally recommended that users of the theme update their installation but it’s also prudent to test whether the updated theme doesn’t cause errors before pushing it to a live website.
Featured Image by Shutterstock/GB_Art