Pichai Says AI Could ‘Break Pretty Much All Software’ via @sejournal, @MattGSouthern

Google CEO Sundar Pichai said AI models could break widely used software and that prices for black-market zero-day exploits may be falling. The comments came during a conversation on the Cheeky Pint podcast with Stripe CEO Patrick Collison.
What Pichai Said
The discussion touched on constraints facing AI infrastructure buildout when Pichai turned to security as a less visible risk.
Pichai said:
“These models are definitely like really going to break pretty much all software out there. Maybe already we don’t know as we sit here and speak.”
Elad Gil mentioned hearing that black market zero-day prices were falling because AI was increasing the supply of discoverable vulnerabilities. Pichai said he was “not at all surprised,” though neither cited specific pricing data.
Pichai framed security threats as a hidden constraint on AI deployment, alongside memory supply and energy. He said the situation would require “more coordination, which is not happening today” and predicted a potential “sharp moment” ahead.
“I don’t think you can wish them away,” Pichai said.
What The Data Shows
Google’s Threat Intelligence Group tracked 90 zero-day exploits used in attacks during 2025, up from 78 in 2024. Nearly half targeted enterprise software, an all-time high.
The GTIG report predicted that AI would “accelerate the ongoing race between attackers and defenders” in 2026. It said adversaries are likely to use AI to accelerate reconnaissance, vulnerability discovery, and exploit development.
While Pichai and Gil described falling black-market prices, industry reporting on the separate commercial-exploit market has shown prices holding or rising in some categories as vendors harden their products.
Why This Matters
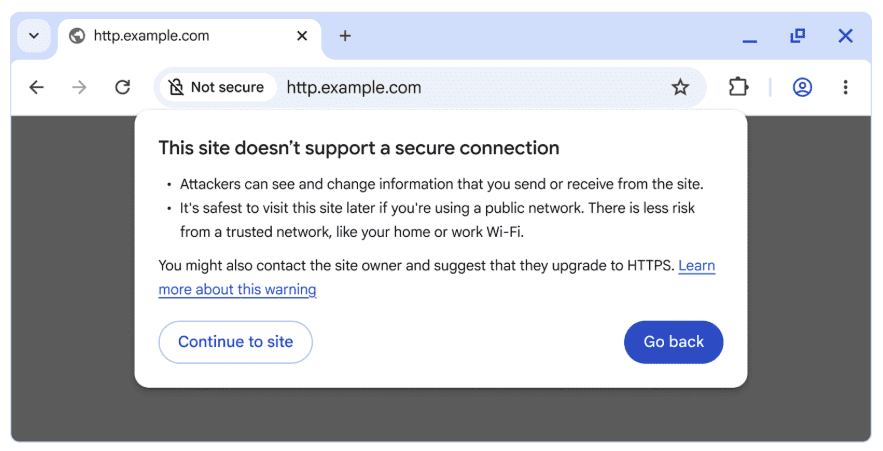
Every website runs on software with potential vulnerabilities. WordPress plugins, server configurations, third-party scripts, and authentication systems are all part of the attack surface that AI-assisted exploit discovery could target faster.
If AI is accelerating the pace at which vulnerabilities are found and weaponized, the window between a flaw existing and an attacker using it gets shorter. That puts more pressure on maintaining current patches and auditing their dependencies.
Google’s threat data shows exploit volume rising and AI accelerating discovery, even if the pricing claim lacks specifics.
Looking Ahead
Pichai’s comments were conversational, not a formal Google policy statement. But they came from someone who oversees both the company’s AI models and its threat intelligence operation.
The gap between AI capability and security readiness is a theme Google’s threat researchers have been documenting with increasing urgency. The GTIG report expects AI to speed both offense and defense going forward.
Featured Image: FotoField/Shutterstock